COREDO – EU Legal & Compliance Services Expert legal consulting, financial licensing (EMI, PSP, CASP under MiCA), and AML/CFT compliance across the European Union. Headquartered in Prague, we provide seamless regulatory solutions in Germany, Poland, Lithuania, and all 27 EU member states.

Since 2016 I have been running COREDO as a company that helps entrepreneurs and finance directors build international structures, obtain licenses and comply with regulatory requirements in Europe, Asia and the CIS. Over this time one of the most “invisible” but critically important elements has become the data processing agreement (DPA) and the entire architecture of working with vendors that handle customer data. Company registration, licensing of payment services or crypto business, AML processes – without a competent DPA and supplier data risk management this construct either doesn’t take off, or over time turns into a source of regulatory problems.
I have compiled in this article our real experience: how we select a model for cross-border data transfers, how we integrate DPIA and DTIA into supplier onboarding, what we set out in DPAs and SLAs, which metrics and KPIs we use to assess vendor security, and how to reduce legal risks with a cloud model across different jurisdictions. COREDO’s practice confirms: a reliable foundation of DPAs, supplier due diligence and transparent processes accelerates projects – from licenses in the EU to expansion into Singapore and Dubai.
DPA in international registration

Map of requirements: EU and Asia

Roles: controller, processor, subprocessors

The controller determines the purposes and means of processing, the processor processes on instructions, subprocessors and the data processing chain must be transparent and formally approved. In the DPA we record the roles and rights of the controller and the processor, as well as flow-down clauses for subcontractors so that the subcontractor’s obligations in the DPA reflect the basic guarantees.
How to conclude a DPA with a SaaS provider
I recommend the following approach, which the COREDO team has refined on dozens of projects:
- Pre-contract stage:
- Conduct Due Diligence of suppliers (vendor due diligence) with a focus on contractors’ certification standards ISO 27001 and SOC 2, encryption policy at rest and in transit, key management (HSM, BYOK), IAM and the principle of least privilege, presence of MFA, SIEM and continuous supplier monitoring.
- Assess the shared responsibility model (IaaS/PaaS/SaaS): where the boundary of responsibility lies for configurations, patch management and vulnerability management.
- Check legal risks of extraterritorial legislation (for example, the CLOUD Act) and reconcile them with DTIA.
- DPA structure:
- Describe the scope of processing, data categories and data subjects, data classification and data minimization, purposes and legal bases.
- Include standard blocks: standard contractual clauses for data transfer (SCC) or BCR/DPF, subprocessing mechanisms and a register of subcontractors, the right to audit and audit frequency (on-site/remote), data breach notification and data security SLA metrics.
- Add conditions for return and deletion of data upon contract termination, data retention and deletion policy, an NDA within the DPA, liability limitations and indemnity clauses.
- Security and SLA:
- Document SLA, RTO and RPO in the DPA for data processing, MTTR metrics and escalation procedures.
- Specify how to ensure contractors’ key encryption (BYOK), requirements for HSM, security logging and integration with your SIEM.
- Set requirements for penetration testing and validation of the contractor’s security, including red team/blue team exercises.
- Data subject rights and controller support:
- Specify how the contractor handles client DSARs (data subject access requests), timelines and communication channels.
- Specify which data will be included in the RoPA and who is responsible for updates.
- Formalities:
- Electronic signature and multijurisdictional validity, translation and legalization of contracts when necessary, legal dispute resolution mechanisms and arbitration, choice of law and jurisdiction.
DPA in international business: SCC, BCR, DPF
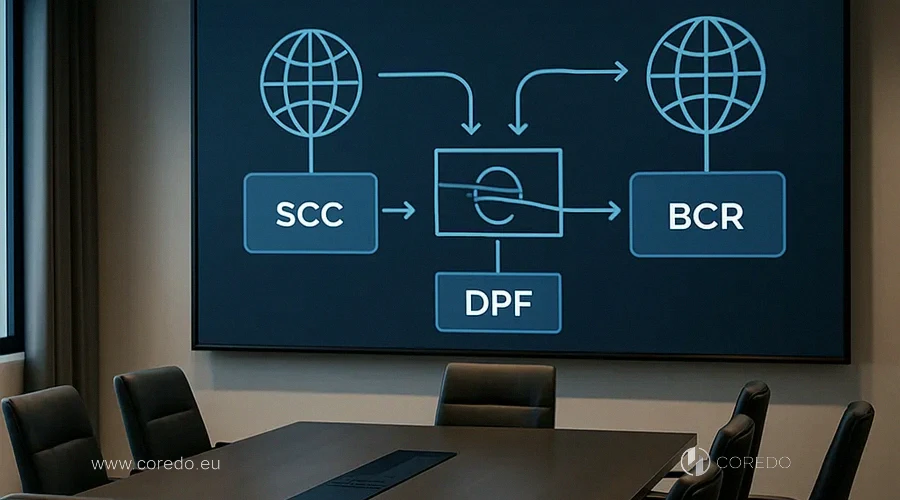
- BCR – if you have a large group across multiple regions and intensive internal transfers.
- SCC – if you are entering into a DPA with an external provider and need flexibility and speed.
- DPF – when your U.S. contractor is certified and you want to reduce the burden on the DTIA.
При передаче в Азию учитывайте локальные режимы и ограничения, а также альтернативные гарантии. Команда COREDO реализовала гибридные модели, где для одних стран применялись SCC, а для других: локальные механизмы с дополнительным шифрованием и псевдонимизацией.
Supplier due diligence and audit
We build a vendor assessment on a risk scale (vendor risk scorecard) across three dimensions: legal risks (transfer mechanisms, legal environment), technical controls (encryption, key management, IAM, MFA, SOC 2/ISO 27001), operational maturity (BCP/DRP, incident management, SIEM). We include KPIs for assessing contractor security: percentage of vulnerabilities closed on time, MTTR for incidents, share of subprocessors with current certification, compliance with RTO/RPO in recovery tests.
Integration of DPIA/DTIA and RoPA
SLA and resilience metrics
Service-level agreements (SLAs) for data security must be measurable. We track:
- RTO/RPO, MTTR, and the frequency of BCP/DRP exercises;
- DSAR processing time;
- data breach notification timelines (in the EU, no later than 72 hours by the controller to the regulator under the DPA, and the processor must notify the controller significantly earlier);
- security service level and SLA metrics for patch management and critical vulnerabilities.
BYOK, HSM and IAM in practice
Encryption at rest and in transit is standard today, but the details determine the outcome. I recommend BYOK with key management in an HSM and clear rotation and revocation procedures. For the cloud – pay attention to the shared responsibility model so that issues around the client’s IAM configuration, MFA, and the principle of least privilege don’t remain unresolved.
DPA enforcement: jurisdiction and arbitration
- We align legal dispute resolution mechanisms and arbitration taking into account presence in the EU/UK and the project’s geography.
- Electronic signatures and multi-jurisdictional validity are confirmed through applicable laws and certificate repositories.
- Translation and legalization of contracts are important when the DPA is included in the package for a local regulator.
- We include NDAs, liability limitations and indemnity clauses with clear liability caps (how to minimize liability in the DPA: a question of balancing risks and service cost).
- For clients in the EU we offer a Data Processing Agreement template (DPA template) adapted to local regulators (Data Protection Authorities) and recommendations from the EDPB/ICO.
Data lifecycle: return, deletion, migration
Compliance ROI for the Board of Directors
- compliance metrics: percentage of compliant vendors and remediation progress;
- cost of non-compliance: potential fines, service downtime, legal costs;
- incident KPIs: MTTR, success rate of recovery tests, meeting RTO/RPO;
- ROI metrics for compliance programs: reduction of cyber insurance premiums, shorter time-to-market in new jurisdictions, faster licensing due to predictable processes.
The COREDO team implemented GRC-based dashboards that consolidate the status of DPA, DPIA/DTIA, data vendor audits and reporting for the board of directors. This is one of those cases where transparency adds speed, not bureaucracy.
COREDO Case Studies: DPA, Licensing and AML
- Fintech in Estonia, handling payments within the EEA. We built an architecture on European clouds with SCCs for separate analytical tools outside the EEA, implemented BYOK and SIEM, defined SLAs and MTTR, and integrated DSAR handling. At the same time we updated the AML policy and KYC providers, executing a personal data processing agreement with subprocessors and a flow-down chain. The regulator accepted the dossier without additional rounds of questions.
- Payment provider in Singapore under the PSA (MAS). The client used a US SaaS for anti-fraud and marketing. We conducted a DTIA taking DPF into account, implemented pseudonymization of marketing data, included RTO/RPO in the DPA, and synthesized test data for pilots. As a result, partner bank approval and PDPA compliance were achieved within the expected timeframe.
- Brokerage company in Cyprus (CIF) with offices in London and Dubai. We established BCRs within the group and SCCs with external contractors, synchronized the requirements of the UK GDPR, DIFC and the Cypriot regulator. We conducted vendor due diligence, set KPIs for assessing contractors’ security, provided for the right to audit and documented an incident response playbook. This allowed the client to scale the operating model without repeated approvals.
- Crypto business in Dubai (VARA). We implemented a strict data minimization policy, ceased using some subprocessors with unclear localization, formalized the terms for data return and deletion upon termination, and conducted a «penalty» security audit of a supplier after an incident at one of the vendors. COREDO’s practice confirmed: preventive measures and rapid forensics protect the license and the relationship with the regulator.
What to check in a DPA before signing
- Role definitions: controller and processor: differences in responsibilities.
- Scope and purposes: data classification and data minimization.
- Transfers: SCC/BCR/DPF, DTIA, Schrems II and implications for transfers.
- Subprocessors: further down the chain and subcontractor register, flow-down clauses.
- Security: encryption, BYOK, HSM, IAM, MFA, vulnerability management.
- Certifications: ISO 27001, SOC 2, PCI DSS for card processing.
- SLA: security service level and SLA metrics, RTO/RPO, MTTR.
- Incidents: data breach notification, incident response playbook.
- Data subject rights: DSAR, RoPA when working with contractors.
- Deletion/return: conditions for returning and deleting data upon contract termination.
- Audit: right to audit and audit frequency (on-site/remote), “penalty audit”.
- Liability: limitations of liability and indemnity clauses, cyber insurance.
- Signature/law: electronic signature and arbitration, translation and legalization if necessary.
Scaling vendor compliance
Business is growing, the number of vendors is rapidly increasing. I recommend:
- segment vendors by risk and apply varying audit frequencies and depth of checks;
- centralize DPA in CLM and link it with GRC, setting up automated vendor compliance monitoring;
- implement tools for continuous vendor monitoring and API integration of compliance evidence;
- train teams and subcontractors, including security training and certification for contractors;
- set compliance metrics: percentage of compliant vendors, time to close remediations, share of vendors with up-to-date ISO/SOC.
DPO when working with contractors
Data Protection Officer – not a ‘checkbox controller’, but a coordinator of data architecture. Their scope includes:
- integration of DPIA and DTIA into supplier onboarding;
- updating RoPA, oversight of data mapping and data lineage;
- coordination of DPA and SLA, engagement with local data protection regulators;
- preparation for audits and responses to data subject requests (DSAR);
- coordination of BCP/DRP and incident exercises;
- use of EDPB recommendations and ICO guidance when working with contractors.
What to do in the event of a data breach by a contractor
- immediate notification of the controller by the processor, initial classification of the incident and activation of the playbook;
- technical isolation, forensics, assessment of affected data categories;
- legal assessment of notification thresholds for data subjects and the regulator, preparation of the notification within required deadlines;
- communication with clients and partners according to an agreed scenario;
- remediation, verification of fixes, and a “penalty audit” in case of material breaches;
- post-mortem and updates to the DPA/SLA, as well as KPIs for MTTR and reliability.
The COREDO team implemented such procedures in several jurisdictions, including the EU and the UAE. After incidents, companies not only regained services but also improved their standing with regulators thanks to transparency and speed.
BCR vs SCC vs DPF in Asia
Clients often ask when to use BCR vs SCC vs DPF. I summarize: BCR — a strategic choice for groups with extensive internal data flows, SCC — a practical tool for external contractors, DPF — an accelerator for the US when certification is available. In Asia it is important to consider local restrictions on cross-border subprocessing and data localization, and to add cryptographic measures, pseudonymization and a clear retention policy.
COREDO: DPA, licensing, AML and growth
In the licensing of payment and crypto projects we parallel three streams: legal configuration (SCC/BCR/DPF), technical security (ISO 27001/SOC 2, BYOK, SIEM, IAM) and an AML pipeline (KYC providers, transaction monitoring, reporting). This approach reduces the time for responses to the regulator, makes partner banks’ due diligence predictable and simplifies scaling to new markets — be it the Czech Republic, Slovakia, Cyprus, Estonia, United Kingdom, Singapore or Dubai.
A reliable foundation for international growth
The COREDO team has, over recent years, guided dozens of projects along this route and knows where clients lose weeks and money, and where – they gain by getting the configuration right. If you need practical, comprehensive support – from DPA templates for European clients to automating vendor compliance monitoring and integrating AML providers into a unified model: my colleagues and I are ready to get involved. Reliable data protection and proper vendor management: it is an investment with a clear ROI, especially in an era of cross-border business and high regulatory demands.