COREDO – EU Legal & Compliance Services Expert legal consulting, financial licensing (EMI, PSP, CASP under MiCA), and AML/CFT compliance across the European Union. Headquartered in Prague, we provide seamless regulatory solutions in Germany, Poland, Lithuania, and all 27 EU member states.

Since 2016 I have been running COREDO through dozens of jurisdictions and hundreds of projects, where accuracy in assessing client risk determines the resilience and scale of the business. The client risk matrix KYC/AML: not a “formal table”, but the core of your compliance and financial security policy. When the COREDO team designs a matrix together with a client from the EU, Singapore, or Dubai, we immediately look at risk appetite, data architecture, operational constraints, and readiness for regulatory inspections. This approach ensures predictable processes, reduces false positive alerts, and provides transparent decision logic for the front office, analysts, and the board of directors.
Risk appetite and client taxonomy

Risk appetite and a correct client taxonomy form the basis of the client risk acceptance matrix and determine which clients and transactions require enhanced controls. For international business this means the need to develop a risk-scoring policy that takes into account regional differences, regulatory requirements and the specifics of client segments.
Risk appetite and risk scoring for business
Risk-scoring policy: it is derived from risk appetite, i.e. the degree of risk management is willing to accept to achieve objectives. I start by formalizing risk appetite along key axes: geography (EU, United Kingdom, Asia, CIS), products (payment services, crypto, forex, acquiring), channels (online, branches, partner networks) and client types (individuals, legal entities, financial institutions). This document creates the boundaries within which the client risk matrix logic is built, and discloses where we apply EDD (enhanced due diligence), where simplified KYC is acceptable and where we introduce stop-lists.
Risk taxonomy: inherent vs residual
A client risk taxonomy is needed to classify risk factors in a common language. I split factors into mandatory (regulatory: sanctions, PEP, UBO), business (segment, turnover, sales channels), behavioral (transactional patterns), and environmental (countries of incorporation and service, correspondent and cross-border risks). For each factor we record inherent risk (the built-in vulnerability before controls), apply controls, measure control effectiveness and obtain residual risk (the remaining risk after controls). This linkage provides manageability and transparent traceability of decisions.
Matrix design and logic
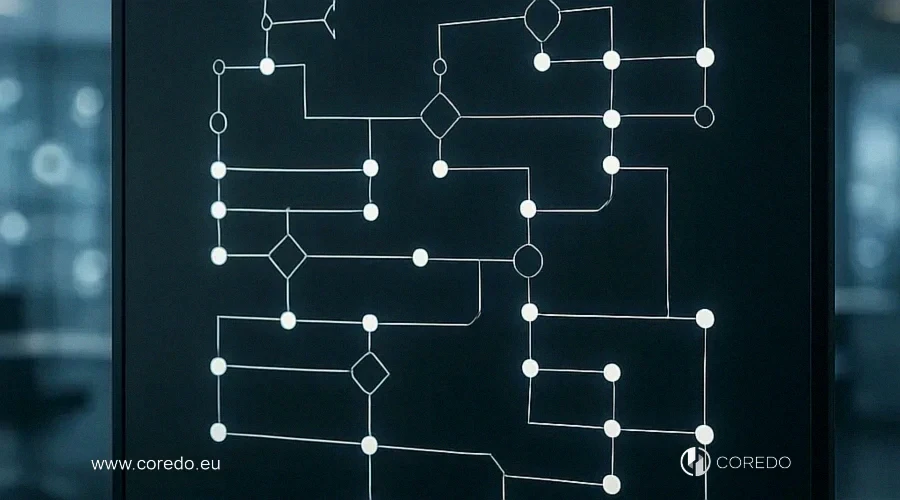
A well-thought-out matrix logic and its design set the structure of criteria used to assess risk and form the client profile. Understanding segmentation and correctly setting thresholds allow qualitative observations to be converted into measurable metrics, making the assessment reproducible and transparent.
Risk assessment and client profile
The client profile and risk assessment are formed based on criteria aligned with FATF and EU AML Directives. For legal entities the key factors remain: ownership structure (UBO), jurisdictions of incorporation and operation, industry (including TBML risks in trading companies), sources of funds, acquisition channels (channel risk), as well as links to PEPs and sanctions. For individuals I add the level of identity verification (eKYC, biometrics), behavioral indicators and fraud patterns (velocity rules).
Client segmentation by risk and KYC
Client segmentation by risk is built on scoring scales and thresholds, where the final category (low/medium/high) governs the depth of KYC and the frequency of profile reviews. KYC control points in the risk matrix include: initial onboarding, activation of a higher-risk product (for example, cross-border payments), reaching a turnover threshold, change of UBO, triggering of adverse media or a sanctions update. Such a design ensures timely EDD for high-risk clients and saves time on low-risk cases.
Risk thresholds, escalation and logic template
Escalation must be clear and predictable. I document RACI: who decides, who approves, who executes. The decision logic template for a client includes: aggregated score (points by factors), data quality (confidence in sources), escalation triggers (sanctions, PEP, TBML signals, offshore structures with nominee directors), and a predefined route in case management. We set risk thresholds taking FP/FN trade-offs into account: the higher the sensitivity to sanctions, the lower the tolerance for FN and the higher the load on the second line of defense.
Risk matrix for legal entities: EU, Asia, CIS
I build the client risk matrix template for legal entities along axes of factors: jurisdiction of incorporation and operational activity, ownership structure (UBO/beneficial owner registries/company transparency), sectoral risk (including financial services, crypto, trade), sanctions and PEP risks, sales channels (online/offline/partners), correspondent relationships and cross-border payments. We assign a weight to each factor taking risk appetite and regulation into account. This is how we configured the matrix for clients registering companies in the Czech Republic and Estonia, as well as for groups with back offices in Singapore and Dubai.
Data source quality checks

Reliable data sources and thorough quality checks are the foundation for correct client verification and minimizing risks in compliance processes. Below we will examine in detail the validation of client information, UBO confirmation, working with registers of owners, and the use of LEI to improve data reliability.
Client checks: Ultimate Beneficial Owner, registers, Legal Entity Identifier
The quality of sources determines the reliability of scoring. I recommend combining official registers of owners (where available), registries of legal entities and LEI, commercial UBO databases, as well as client documents with independent verification. In entity resolution and data deduplication we take into account transliteration and fuzzing: errors in spelling names and addresses lead to misses in match algorithms. COREDO implements a double loop: machine matching and manual validation for “grey” matches.
Sanctions lists, PEP and adverse media
Sanctions lists (OFAC, EU, UN) and PEP play a central role in the AML risk matrix. I include sanctions in a “hard” scoring module, where even a “possible match” triggers escalation. Adverse media screening complements the picture, especially for sectors with reputational risks. We assess correspondent and cross-border risks by jurisdictional combinations and payment types, which is particularly important when obtaining payment and forex licenses.
eKYC identity verification and biometrics
Remote onboarding requires reliable identity verification. I use eKYC with document inspection, liveness, biometrics and qualified electronic identification means in accordance with eIDAS. For corporate clients I enable verification of signatories’ mandates and their PEP/sanctions status. This stack increases scoring accuracy and reduces fraud risks without increasing friction in the process.
Automation of scoring algorithms
In scoring systems both rule-based mechanisms and machine learning play a key role; it is their combination and the automation of decision-making that form effective evaluation models. Below we will successively consider rule-based approaches and specific ML tools such as logistic regression and gradient boosting, which improve accuracy and scalability.
Rule-based and ML approaches
Scoring algorithms range from rule-based matrices to ML models. Rules are convenient for transparency but are limited in the complexity of patterns. ML models (logistic regression, gradient boosting) allow accounting for nonlinear interactions of factors and better calibrating the client’s risk probability. I prefer a combined approach: rules for regulatory «hard-stops», algorithms for the probabilistic component and fine-tuning the FP/FN trade-off.
Explainable AI and XAI, model governance
Explainability and XAI are mandatory for regulatory reporting and dialogues with auditors. I include global and local explanations: the contribution of factors to the overall score and the reasons for a specific decision on a client. Model governance records the lifecycle: development, validation by an independent team, backtesting, drift monitoring and an update plan. Concept drift in compliance is inevitable, so we create feature stability metrics, retraining triggers and a procedure for approving changes through the risk committee.
CRM integrations, APIs, and payment gateways
Integrating the risk matrix with CRM and payment gateways via API provides real-time scoring. I recommend a centralized case management where the full log of decisions and correspondence is stored, as well as case routing by SLA. It is important to provide for «synchronous» responses (fast onboarding) and «asynchronous» checks (EDD) to maintain business speed and compliance depth.
Data architecture and data lineage
The data architecture must support data lineage and full traceability of decisions. I require that each metric and factor have a source and version, and that the audit log reflect changes to rules and the model. This speeds up debugging, reduces operational risk and increases auditors’ confidence. Technologically we use entity resolution with fuzzing and transliteration rules to minimize matching errors on names, addresses and identifiers.
Reducing false positives

Monitoring user behavior is key to the timely detection of anomalies and attacks, and a proper reduction of false positives increases detection accuracy and reduces analysts’ workload. In the following subsections we’ll examine how transaction analysis, velocity rules, graph databases and link analysis help build a robust monitoring system and minimize false alerts.
Transaction analysis and velocity rules
Behavioral monitoring complements the KYC profile. I configure velocity rules (speed and limit restrictions), behavioral profiles, and also graph/link analysis to detect networks and hidden connections between clients and counterparties. Graph databases strengthen AML analytics in parts related to structuring schemes and «mules».
Clustering, anomalies, TBML
For new schemes and TBML I use unsupervised learning: clustering and anomaly detection based on invoice attributes, supply routes and atypical geographic combinations. Such models do not replace rules but complement them, suggesting new patterns for experts. This is especially useful in international trade when long supply chains hide beneficiaries.
Threshold tuning: trade-off FP/FN
Reducing false positives is one of the main drivers of ROI. I calibrate thresholds on validation samples and add secondary features that separate normal activity spikes from fraud. To manage false negatives (FN), we strengthen «red flags» related to sanctions, PEP and TBML, and regularly review their sensitivity. This balance provides resilience against regulatory claims and does not overload analysts.
Post-onboarding risk monitoring
A client’s risk profile changes. I require mandatory profile reviews based on events (change of UBO, increase in turnover, new countries) and on schedules (for example, an annual re-risk assessment). Such discipline leads to a reduction in residual risk and strengthens the position during external audits.
Compliance with the regulatory framework
The regulatory framework sets the foundations of legal and organizational requirements, and compliance with it provides protection against sanctions and reputational risks. Below we will examine the key international standards and approaches: from FATF recommendations and EU AML Directives to ISO 31000 for risk management and the COSO internal control framework.
FATF, EU AML Directives, ISO 31000, COSO
risk matrix AML relies on FATF recommendations and the requirements of the EU AML Directives. The risk assessment methodology aligns with ISO 31000 and COSO principles for risk management. These standards set the language and expected rigor of documentation, testing and reporting, which is important for licensing and inspections.
The impact of GDPR on AML processes
GDPR affects the collection and storage of data for the risk matrix. I document lawful bases, data minimization, retention periods and data subject rights. It is important to manage access and encryption, taking into account the sensitivity of sanctions, PEP and biometric data. GDPR breaches complicate AML processes, so the architecture must ensure privacy by design.
SAR/STR and interaction with regulators
A strong matrix speeds up the preparation and filing of SAR/STR. I recommend keeping a ready package of evidence for each case: scoring logs, adverse media, a connection graph, correspondence and decisions. Being prepared in advance for regulatory inspection and external audits reduces stress and cuts costs. At COREDO we train client teams through mock audits and tabletop reviews.
Organization and Roles
A well-designed organization of processes and a clear allocation of roles are critical for effective compliance and risk management. In the following subsections we will consider the role of the Chief Compliance Officer, the application of the RACI matrix, and the specific responsibilities of the compliance director to understand who is accountable for what in practice.
Responsibilities of the Compliance Director
The CCO is responsible for policy, the risk matrix, model validation, and interaction with regulators. I recommend using RACI for all stages: data collection, scoring, escalation, investigation, reporting. The compliance director’s responsibilities include approving risk thresholds, monitoring KPI/KRI, incident management, and the annual update of the risk appetite.
Staff Training and Process Adoption
People are the key to success. I set up training on KYC/AML, working with case management, and the escalation plan with case prioritization. The instructions describe a template of decision-making logic so that analysts provide reasoned and repeatable conclusions. Regular feedback exchange accelerates the calibration of rules and models.
Frequent mistakes and failures
Errors in decision-making processes lead to systemic breakdowns and frequent failures in risk management, which directly affect the quality of customer segmentation. In the following subsections we will examine typical missteps when building a risk matrix and common mistakes in customer classification to understand how to prevent them.
Errors in the risk matrix and classification
Typical problems: unclear risk appetite, overcomplication of factors without calibration, ignoring data quality and the absence of XAI. I have seen matrices without drift control become outdated quickly, and thresholds without buffer zones simply produce rejections. Errors in customer classification often occur due to weak entity resolution and transliteration issues, which are addressed by combined algorithms and procedural validation.
Money laundering through weak matrices
Weak matrices provide a window to circumvent sanctions through offshore structures and nominee directors. We reviewed cases where non-bank financial services accepted clients with “clean” fronts, ignoring link analysis and adverse media. Graph analytics and UBO checks across multiple sources close this gap. When COREDO strengthened the matrix for a client in the EU, profile enrichment and rule revision uncovered hidden ties to sanctioned persons and prevented fines.
Implementation/calibration/stress-testing
For the risk matrix to work in real-world conditions, it’s important not only to implement it correctly but also to systematically calibrate metrics and prepare for targeted stress-testing of scenarios. Below: a practical checklist for implementing a risk matrix and proven best practices for step-by-step tuning and validating solution resilience.
Risk matrix implementation checklist
- Define the risk appetite and document the risk-scoring policy with usage examples. This will create a basis for communications with regulators and internal teams.
- Build a risk taxonomy and separate inherent and residual risk with an assessment of control effectiveness. This will allow you to manage risks in a targeted and measurable way.
- Formulate criteria and weights, and define KYC and EDD checkpoints. This will speed up onboarding and reduce decision variability.
- Choose data sources, set up entity resolution and fuzzing. This will reduce false positives and improve match quality.
- Decide where to use rules and where ML applies, and ensure XAI and model governance. This will provide accuracy and transparency simultaneously.
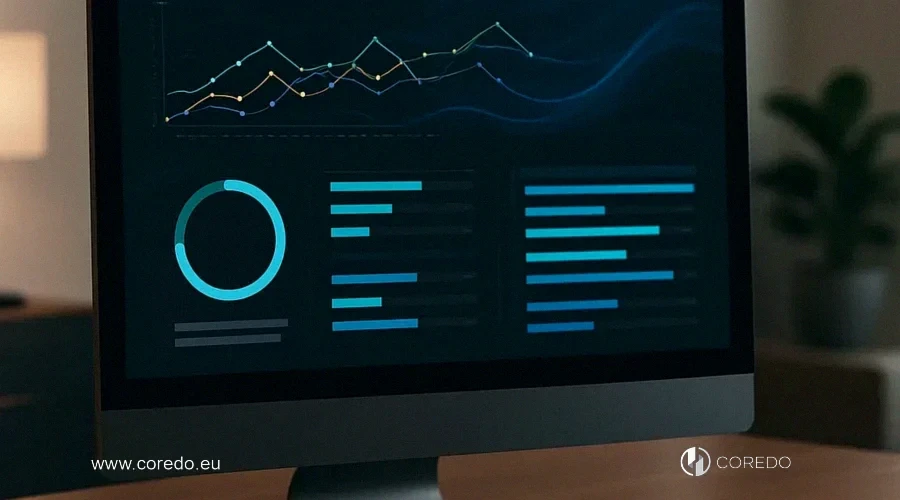
- Include API integrations, case management and visualization of the risk matrix in BI dashboards. This will provide real-time management and a clear analytical picture.
- Run a pilot, calibrate thresholds, set up an escalation plan and training. This will shorten time to value and reduce operational risks.
How to test a risk model: KPI, AUC
Testing and calibration are continuous processes. I use holdout samples, cross-validation, backtesting on historical cases, and monitoring the stability of the scoring distribution. KPIs include: average onboarding time, share of automatic approvals, share of escalations, AUC, precision, recall, as well as regulatory metrics — the proportion of correctly filed SAR/STR. KRIs reflect early signals: an increase in FNs for important scenarios, feature drift, spikes in FPs in specific segments.
Stress and scenario testing
Stress tests check the matrix under extremes: mass updates to sanctions lists, a surge in risky transactions, changes in sales channels, new markets. I model shocks and estimate residual risk, and also test control effectiveness and the throughput capacity of investigations. Scenario testing helps prepare an escalation plan and resource reallocation in advance.
ROI and economics
Business economics and the ROI metric are key criteria when evaluating the effectiveness of management initiatives. Let’s examine how implementing a risk matrix affects return on investment and which performance metrics allow you to accurately measure its benefit.
ROI and risk matrix metrics
The ROI from implementing a risk matrix consists of reduced manual work, fewer false positives, faster onboarding, and reduced penalty risks. In my experience BI dashboards show the economic effect by month: savings in analyst hours, lower case cost, an increase in the share of clients who completed onboarding within SLA. We tie the risk matrix performance metrics (KPI) to business goals so compliance does not operate separately from P&L.
Reducing operational costs in KYC
Rule optimization and flexible segmentation reduce investigation costs and ease the load on the second line of defense. When COREDO simplified rules in the “green zone” and tightened them for EDD, the overall workload decreased and the quality of investigations improved. It’s important not to chase an “ideal model”, but to build a pragmatic improvement cycle supported by data and feedback from teams.
COREDO Case Studies
In COREDO case studies we analyze real practices of registering legal entities in the EU, identifying key risks and common mistakes. Below is a risk matrix that helps systematize threats, assess their likelihood and choose appropriate mitigation measures.
Risks of Registering Legal Entities in the EU
For a holding company registering companies in the Czech Republic and Estonia for payment services, we set up an AML risk matrix and integration with registries, LEI and sanctions sources. Industry risk and cross-border flows were accounted for through weights and a behavioral module. Dashboard visualizations allowed the board of directors to see the distribution of risk across the portfolio and make strategic market decisions.
Risk Matrix for Companies in Asia and the CIS
For a group operating in Singapore and several CIS countries, we implemented segmentation by sales channels and TBML control for trade flows. We included adverse media screening in local languages and expanded UBO checks through multiple sources. Residual risk was reduced by a measurable amount, and the licensing authority accepted the compliance policy without comments.
Licenses and Integration of the Matrix into AML
While preparing for crypto and payment licenses in Cyprus, Estonia and the United Kingdom, the COREDO team demonstrated to regulators the matrix logic, XAI explanations and governance models. We demonstrated integration with CRM, payment gateways and case management, as well as readiness for SAR/STR and external audits. This level of transparency accelerated Licensing and set a standard for operational control.
Change management and resilience
Effective change management: a key factor for the long-term resilience of systems and business processes. The following discusses approaches to managing regulatory changes, model updates and monitoring concept drift that help maintain adaptability and compliance with requirements.
Regulatory changes and concept drift
The regulatory environment changes, as does customer behavior. I implement a regulatory change management process: monitoring requirements, impact assessment, document updates, team training and releasing changes. For models I establish drift monitoring and a retraining schedule, as well as a ‘canary’ — a small share of traffic for a safe test of updates. This approach prevents risk accumulation and maintains compliance with requirements.
Reporting to the board: KCI/KRI
The board needs clear indicators: KCI/KRI on onboarding, sanctions matches, EDD, cost of investigations, SLA for cases and model stability. I prepare quarterly reviews with visualizations of the risk matrix, distribution dynamics, AUC/precision/recall metrics and a roadmap of improvements. This builds trust and helps align the risk appetite with growth ambitions.
Practical value and the next step
The AML risk matrix is a management tool that connects strategy, data, models, and operational procedures. When I design such a system with the COREDO team, the goal is one: to turn compliance from a ‘brake’ into an accelerator of growth, where risk appetite is clear, decision logic is transparent, and processes withstand audits and scaling. We achieve this through precise criteria, reliable sources, explainable AI, strong governance, and regular calibration.